Stop spam before it reaches the mailbox
Stalwart's spam and phishing filter is part of the server, not an extra daemon to install and tune. It runs at SMTP time, so unwanted mail is stopped before it reaches a mailbox; it learns from user feedback; and it combines a statistical classifier, public blocklists, phishing heuristics, sender reputation and AI analysis into a single score.
A spam filter that learns from your users.
The classifier learns continuously from what your users do. Every time a recipient marks a message as spam, marks it as ham, or moves it out of the junk folder, the filter updates the score for the patterns in that message. Senders already in a recipient's address book are pre-classified as known correspondents, which removes a common class of false positive without operator intervention.
- FTRL-Proximal linear classifier.
- Standard feature hashing or cuckoo feature hashing for large deployments.
- Continuous online training from user feedback.
- Address-book signal: senders in a recipient's contacts are weighted toward ham.
- Encryption-at-rest privacy setting for training data.
AI for the messages that need a second look.
Some phishing and social-engineering messages slip through any classifier that only counts patterns. Any OpenAI-compatible endpoint works: hosted (OpenAI, Anthropic), self-hosted (Llama via LocalAI, vLLM) or anything else that speaks the same API. Trusted Sieve scripts call the model at SMTP data time; users with the right permission can call it from their own scripts too.
- LLM module for the spam classifier.
- Sieve functions for AI analysis.
- OpenAI, Anthropic, or self-hosted endpoints.
Boosted spam detection with collaborative filtering.
Public blocklists and collaborative filtering catch a large slice of automated spam before anything else has to look at the message. Stalwart queries DNS-based blocklists for the connecting IP, and for the domains and URLs lifted from the message body, so even subtle threats are detected. Pyzor adds collaborative digest-based filtering against a global network of contributors, so spam patterns identified anywhere quickly inform your filter.
- IP, domain, URL and content-hash blocklists.
- Pyzor digest-based collaborative filtering.
- Tunable per-source thresholds and weights.
Stop forged senders before they reach the mailbox.
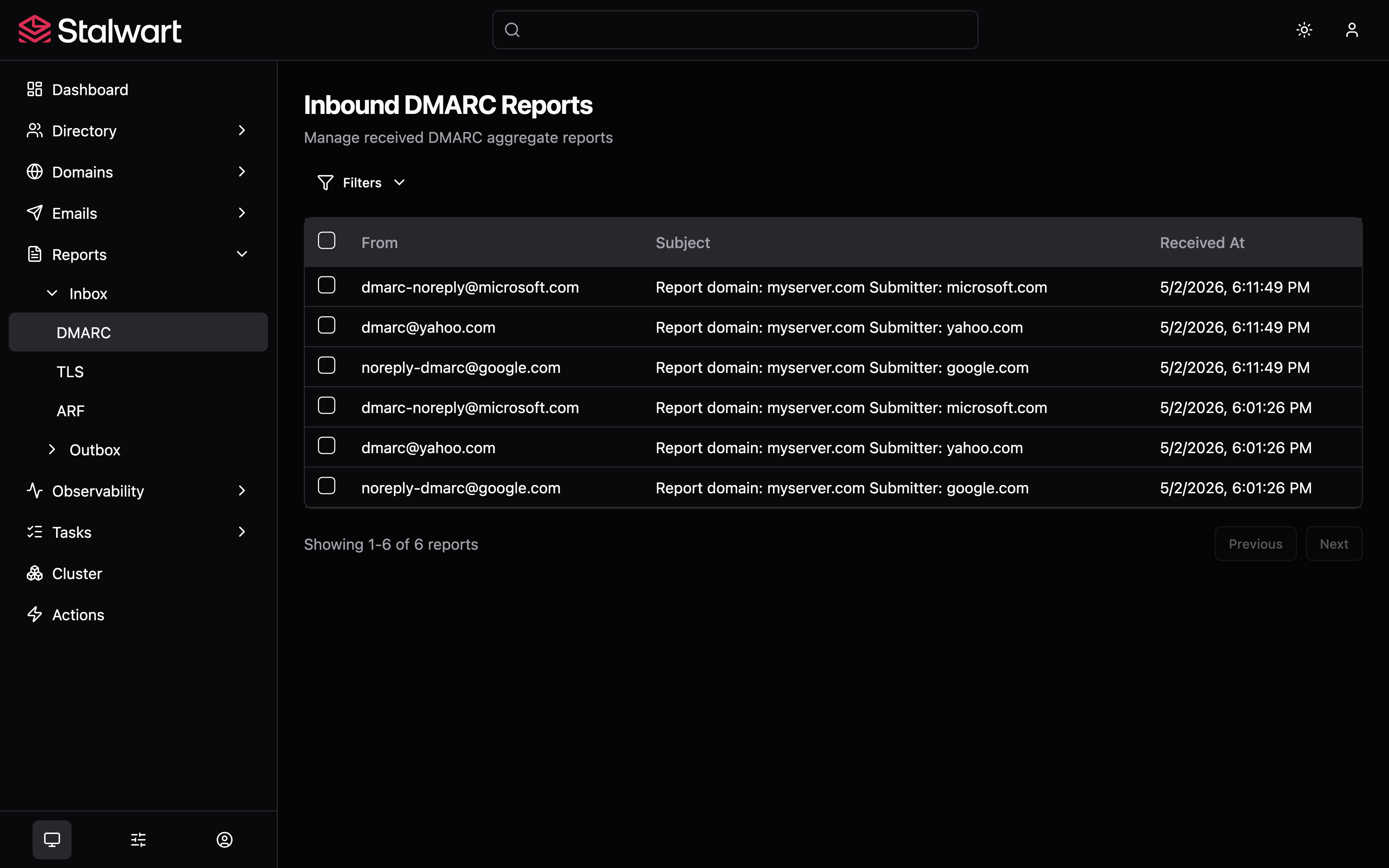
Most phishing forges the From address. Stalwart runs DMARC alignment, SPF policy evaluation, DKIM signature checks and ARC chain verification on every inbound message, and feeds the result into the same score as the rest of the filter, so a message pretending to come from your bank, your CEO or a customer rarely lands in an inbox.
- DMARC alignment checking and reporting.
- SPF, DKIM and ARC verification on inbound mail.
- Tag-based scoring shared with the classifier and blocklists.
Phishing detection, beyond keywords.
Phishing rarely relies on the words in the body; it relies on the structure around them. Stalwart spots the techniques attackers actually use, including visually-confusable Unicode characters in URLs, mismatches between the display name and the From address, and sender domains that imitate the recipient's own domain. Trusted-reply tracking recognises genuine reply threads to a message your user previously sent, so a real reply is not treated with suspicion.
- Homograph URL detection.
- Sender spoofing and lookalike-domain detection.
- Trusted-reply tracking on outgoing messages.
Reputation built from your own traffic.
A sender's reputation should reflect how they have behaved in your traffic, not just what a public list says. Stalwart tracks reputation across four axes at once: the source IP, the network (ASN) it belongs to, the sending domain, and the individual sender address. Each axis contributes a learned score that updates with every message processed, so spam scoring becomes more accurate the longer the deployment runs.
- Per-IP, per-ASN, per-domain and per-email reputation scoring.
- ASN and GeoIP enrichment for headers and reporting.
- Greylisting for unknown senders.
- Spam traps that auto-train the classifier on what they catch.
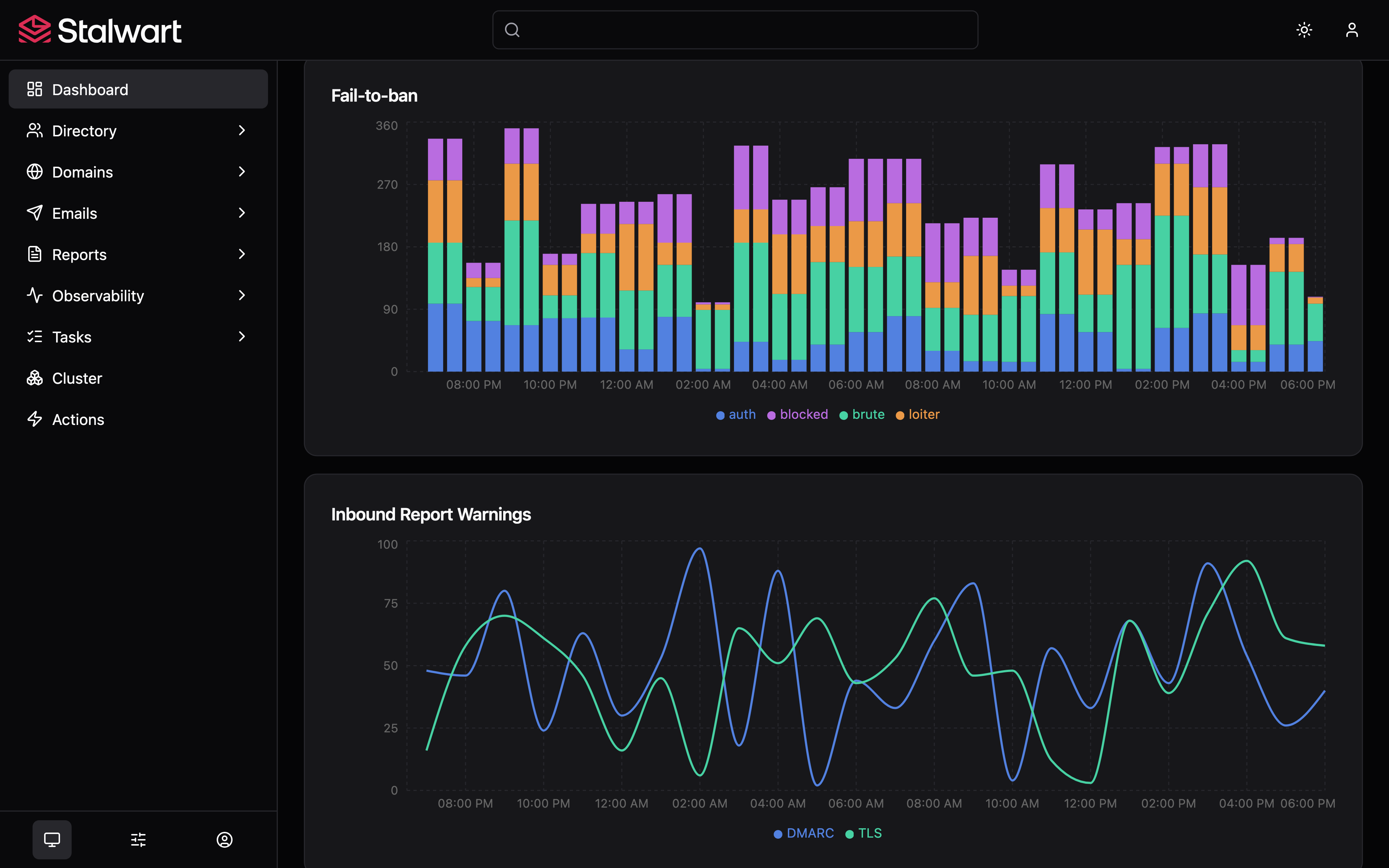
Brute-force and probing attacks blocked automatically.
Stalwart watches for abusive behaviour and bans source IPs on its own, so an operator does not have to install and tune a separate fail2ban-style tool alongside the server. Four independent categories of abuse are tracked, with a configurable threshold for each. Authentication tracking keys on both the source and the login name, so a distributed brute-force attempt against a single account is caught even when the attacker rotates IPs. Every ban records its reason and expiry; manual entries from the web admin or CLI live in the same table.
- Authentication failures.
- SMTP relay and recipient-probing abuse.
- Loitering connections.
- Port and exploit-URL scanning.
Bring your existing Rspamd, SpamAssassin or ClamAV.
If your team already runs a content-filtering stack and wants to keep it, the built-in filter sits next to it instead of replacing it. Milter handles Rspamd, SpamAssassin and ClamAV without changes; MTA Hooks expose the same lifecycle over HTTP and JSON for filters that prefer a web protocol.
- Milter for Rspamd, SpamAssassin, ClamAV and any sendmail-compatible filter.
- MTA Hooks for HTTP + JSON filters.
- Per-stage invocation across every SMTP phase.